What happens when security experts, private investigators, legal professionals and policymakers spend a full day talking about insider threat? You get a room full of people realizing that this problem is bigger, more cross-functional, and more urgent than most organizations currently acknowledge. Here's what stood out.
Setting the Scene
On March 4, 2026, EPOB vzw hosted its first dedicated Insider Threat Day in Oostende - a full-day event bringing together professionals from security, investigations, legal, HR, and governance. Wildcard Group was invited to contribute to the program with a morning panel discussion, a keynote on screening in high-trust environments, and an afternoon deep-dive session on digital investigations and threat-informed defence.
What made this event different from the usual cybersecurity conference wasn't the technology on display - there wasn't any. It was the composition of the room. This wasn't a vendor showcase event. It was a working day where different disciplines came together to discuss a problem that none of them can solve alone.

1. Most Organizations Don't Know Where to Start
The morning kicked off with a panel discussion on insider threat readiness in Belgian organizations. The central question was straightforward: are we prepared for what can go wrong internally, or do we only respond once the damage is done?
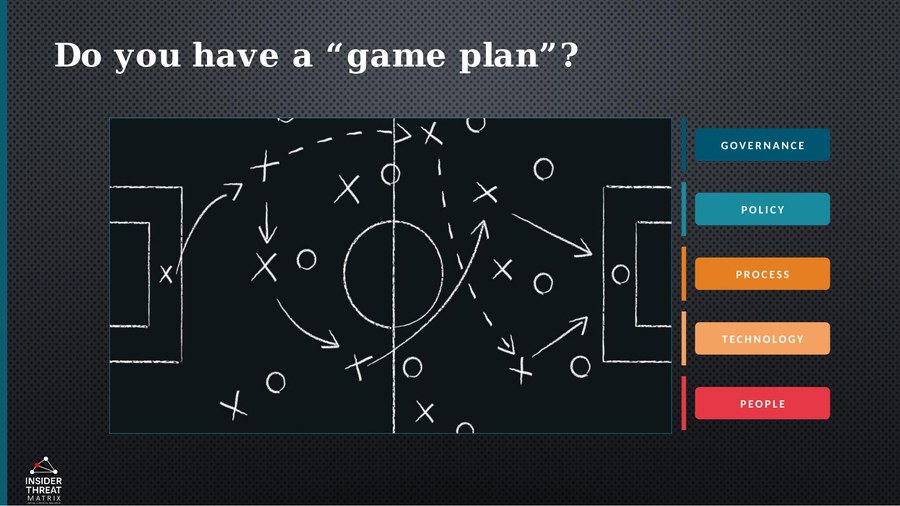
The answer, based on the discussion with attendees and panelists, was sobering. Most organizations treat insider threat as a subset of cybersecurity - something that firewalls and endpoint detection should catch. But insider risk doesn't start with a technical indicator. It starts with access, trust, and human behavior. A key insight rapidly became clear: the biggest gap isn't technology - it's governance. Who owns insider risk in your organization? In most cases, nobody does explicitly. It falls somewhere between HR, security, IT, and legal - and in that gap, threats go undetected.
2. Screening Is a Lifecycle Event, Not a Checkbox
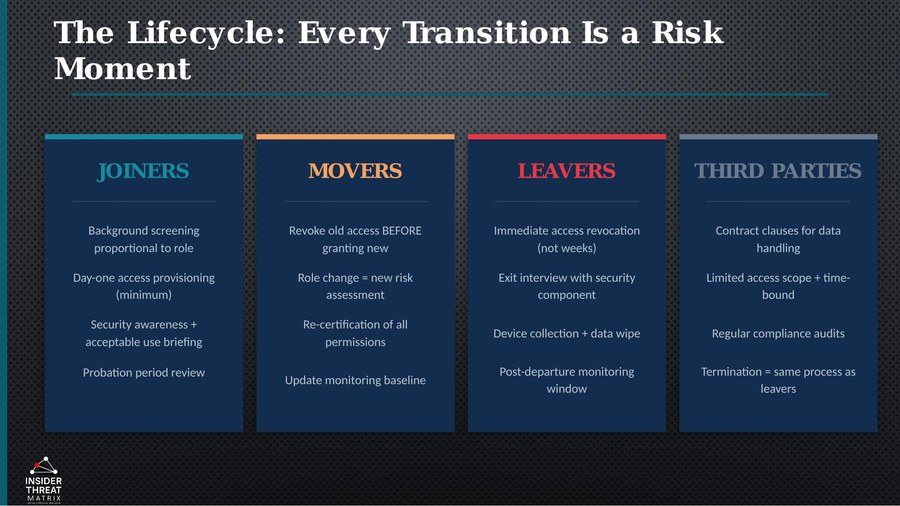
In our keynote, we explored why screening in high-trust environments needs to be rethought. The traditional approach - a background check at hiring, maybe a periodic review for clearance holders - leaves organizations exposed during the periods that matter most: role changes, access escalations, personal crises, and offboarding.
Insider risk is a lifecycle event. It begins long before the first incident and continues long after an employee leaves. Carnegie Mellon's CERT research on thousands of real-world cases consistently shows that warning signs are present well in advance - but only if you have processes in place to detect them. Most organizations don't. They screen once, trust indefinitely, and investigate only after the fact.
The keynote proposed a different model: proportional, continuous, and evidence-based screening that adapts to risk levels throughout the employment lifecycle. Not surveillance - structured awareness. The kind that allows you to intervene early, before trust is broken and before damage is done.
3. Investigations Need to Be Designed Before They're Needed
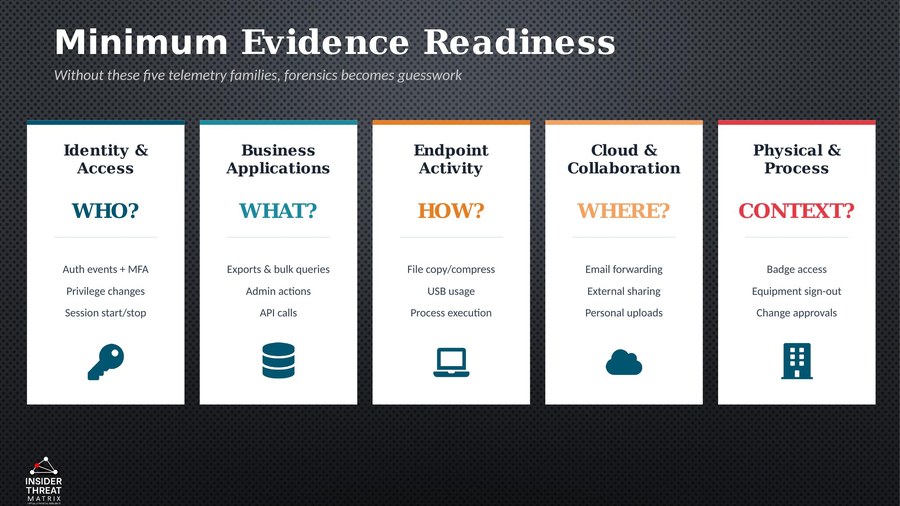
The afternoon session, delivered together with Tjebbe Van Quickenborne of i-Force, focused on what happens when prevention fails and an investigation becomes necessary. The core message: you cannot investigate what you haven't prepared to investigate.
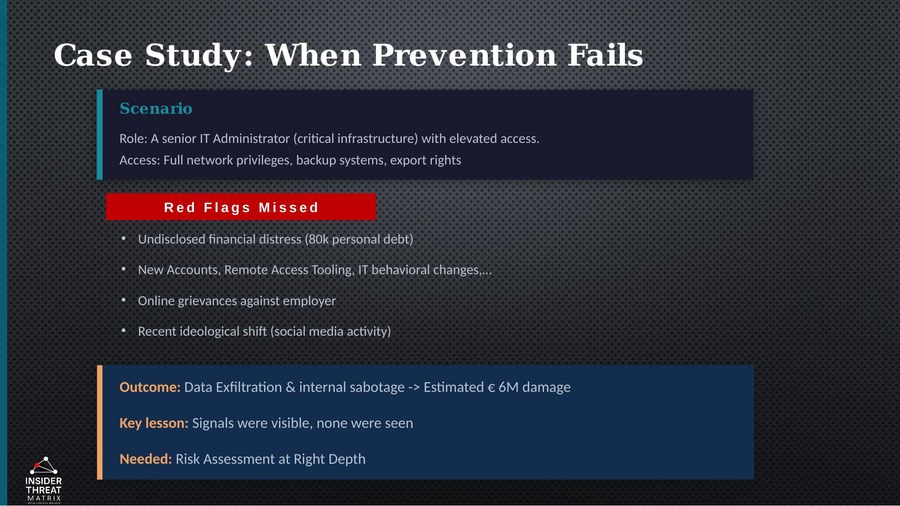
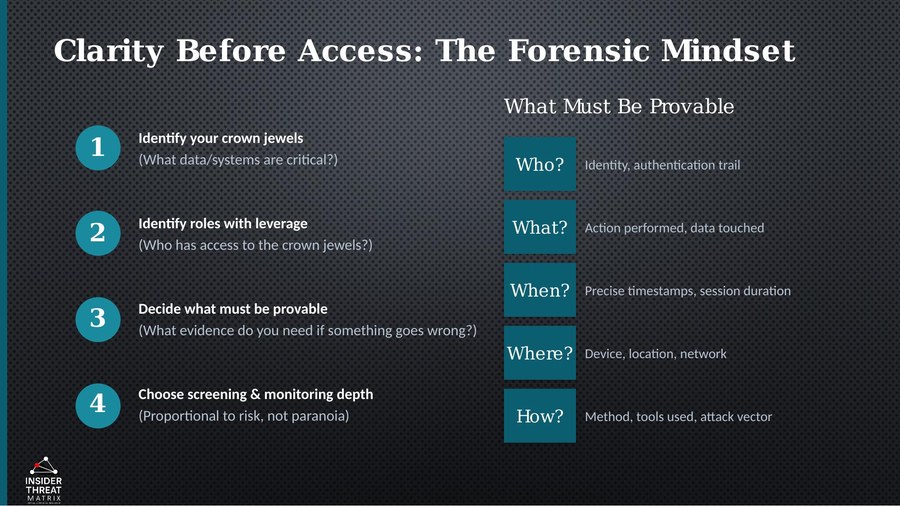
Too many organizations discover during an active insider investigation that their logging is insufficient, their evidence collection isn't forensically sound, and their chain of custody doesn't hold up under scrutiny. At that point, it's too late. Evidence that could have been decisive is inadmissible. Timelines that should have been airtight have gaps. Decisions that seemed justified at the time can't be defended after the fact.
The session approached digital investigations not from a tools-and-technology perspective, but from the perspective of evidence, proportionality, and operational resilience. What do you need to organize, record, and log today so that tomorrow you can demonstrate facts, support decisions, and hold up legally? That's not a question most organizations are asking - but it's one they should be.
4. Insider Threat Requires a Multidisciplinary Approach
If there was one theme that ran through the entire day, it was this: insider threat is not a problem that any single discipline can solve. Security teams see behavioral anomalies but lack legal context. HR holds the employment relationship but doesn't always understand the technical indicators. Legal knows the regulatory framework but isn't involved in early detection. Investigators arrive after the fact and work with whatever evidence happens to exist.
The EPOB event brought all of these perspectives into the same room - and the result was a kind of conversation that doesn't happen often enough. Policymakers heard from investigators what breaks down during a real case. Investigators heard from governance professionals about the constraints they operate under. Security practitioners heard from legal experts about what constitutes proportionate monitoring under Belgian and European law.
This isn't a luxury. It's a prerequisite for any organization serious about managing insider risk. Building an insider threat program in disciplinary silos produces a program that works on paper but fails in practice. The organizations that get this right are the ones that bring these disciplines together - not once a year at a conference, but structurally, as part of how they govern risk.
5. We Need This Conversation More Often
Perhaps the most striking observation from the day was simply how rare this type of event is in Belgium. Insider threat as a discipline is well-established in the United States, where federal mandates have driven organizational programs for over a decade. In Europe - and certainly in Belgium - it remains largely under the radar. Most organizations acknowledge the risk in principle but haven't formalized a response. There is no regulatory obligation specifically requiring an insider threat program (though NIS2 and DORA push in that direction), and the expertise to build one is scarce.
The EPOB Insider Threat Day demonstrated that the appetite for this conversation exists. The room was engaged, the questions were sharp, and the feedback was clear: this needs to happen more. Not as a one-off event, but as a sustained dialogue between the disciplines that have a stake in getting insider threat right.
Looking Ahead
The insights from this event reinforce what we see in our own practice: organizations that treat insider threat as a structural risk - rather than an IT problem or a compliance checkbox - are the ones that build programs that actually work. Programs that detect early, investigate soundly, and withstand legal and operational scrutiny.
In the coming weeks, we'll be sharing more of our thinking on insider threat management, evidence readiness, and threat-informed defence. Not as theory, but from what works in practice.